Symantec Endpoint Protection Crack 15 With Free Download 2023
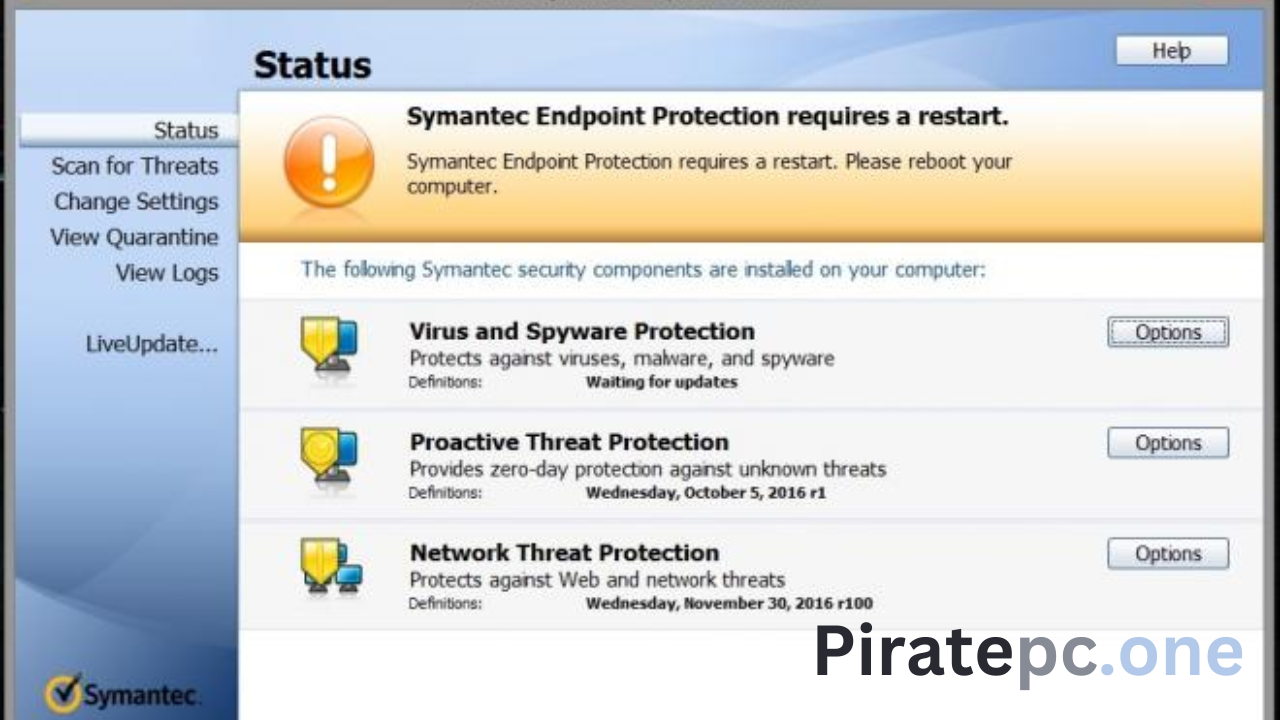
Symantec Endpoint Security 15 Crack Extreme single-agent endpoint security that fits the world. According to Gartner, Symantec is positioned as the most effective and valuable magic dia software tool for immediate deployment. The software’s main feature is a built-in recovery tool that can create an auto-bootable USB flash drive containing the full version of Symantec Malware Removal Tool as a zone and several network antivirus programs. Use the full and unlimited user version of the braking system. Symantec Endpoint Protection Keygen 2023 protects us better. Symantec Endpoint Security is one of the world’s leading security companies. This software offers advanced security, software, and privacy with updates and performance improvements for real situations and events. Symantec Ultimate Protection License Key 2023 is an.OS security product. Full backup provides excellent protection for your computer. The organization does not develop Symantec Antivirus Business and its commercial versions of the antivirus program.
Symantec Endpoint Protection With Crack:
It will improve the efficiency and productivity of your system. It uses the latest facial recognition technology to help identify who is accessing your computer without your knowledge. This software speeds up the overall performance of your device or tool. Maintained garage database and records stored on the server. People keep their records permanently where they live. Organizations around the world come to Symantec for strategic planning. A built-in response to protect enlists, clouds, and infrastructure from small-scale attacks. Remove viruses from devices.
It’s designed for maximum performance that helps your device run faster and longer. It provides a cleaner web experience with taser glitches across various operating systems, including Windows, Linux, and Mac OS X. It’s loaded with tools and features. Continue […] Change website and browser settings. Work is delayed or stopped due to the slow pace and high cost of equipment. The server stores and stores the data. You should disable any antivirus software you have installed. Semantic Endpoint Security should be the best software for your business.
Better information security is achieved without connecting users to operating systems via VPN. Norton Symantec Endpoint Protection 2023 protects virtual assets and performs tasks and updates without scanning images and photos, detecting virtual clients, or directly managing them. Customers can avoid spyware and malware by using secure data.
Download Symantec Endpoint Protection 14 Full Crack:
Symantec Endpoint Protection is an advanced and powerful software package that provides edge protecPeople’sh security measures and protects computers and systems against all types of viruses. This rule applies to all computers and machines. People’s productivity is declining day by day. Protect against all known cybercrime attacks from a single platform. The machine works 100% correctly and without any problems. Humans can have many users and traits that can be useful in human applications.
The new version of Symantec Endpoint Protection is more portable and practical on users’ devices with any device. Symantec Endpoint Protection has gone beyond network infrastructure protection. Save shared browser storage and instantly view photos offline. Symantec Endpoint Protection Antivirus combines multi-layered vulnerability and malware protection with cloud-based management. Fully compatible with Windows machines with reference numbers and valid licenses.
Download Symantec Endpoint Protection Manager 14 Full Crack With License Key
Symantec Protection 2023 license key provides better protection for customers. Protect against recent and unknown vulnerabilities: internal software and target events. Manage basic configuration for centralized control of analogue and electronic assets. Tuning and handling have been improved. It is the most famous security software company in the world. Main Software Security There is a lot of free antivirus software. This software guarantees the best protection of your operating system and personal freedom on the internet.
It is popular because of the quality of the user interface and the fact that computer-literate people do not need to be trained to use this ultra-modern software model. One more thing, targeted attacks give you the element you it’s to survive. Encourage your employees to work with confidence. While many think they are on their feet, we do just about everything at Symantec. The mixing of clouds and particles reduces the phase contrast. You hope it’s a strong foundation for your business.
Symantec Endpoint Protection 2023 Crack is an excellent advancement in emotional manipulation, resilience, awareness, and workplace responsiveness. According to Gartner, Microsoft is at the forefront of performance and visibility magic for local alarm systems. It is an enterprise access control product in various configurations combined with the entrepreneurial spirit. Some onboard storage is the main benefit of such a product, which Symantec Endpoint Protection can use to create flash drives to remove various antivirus and viruses. The primary tool is primary, but most distributed security software does not require a signature. Leverage every version of business technology as it evolves.
Critical Features Of Symantec Endpoint Protection
- The number of attacks is reduced. Classify vulnerabilities and threats and prioritize maintenance based on severity and several affected devices. It integrates with Active Directory for failover and failover. Provides resource management, process isolation, and configuration management, including virtual and static resources.
- Prevent attacks. Protect files and memory from attacks, use machine learning to detect new and unexpected attacks, and prevent attacks in real-time. In addition to traditional signature-based methods, malware is detected using automated processes, sandblasting, suspicious detection, and deletion. Files. Quickly configure the search and customize it for each device.
- Hack to protect. Detect malware using phishing messages, certificates, network shares, network requests, and negative results to prevent attackers from access to physical IT resources. Soft slopes complicate the machine—Enterprise Active Directory manager.
- That is the answer. Symantec’s database uses 3,000 security scans to quickly identify threats and provide information about attackers, tactics, machine failures, and business recovery. Purchase Procedures. Get detailed information using the MITR ATT & CK method to detect attacks before they are found. Provide tools for detecting threats and security parameters. This creates a safety net: a simple last resort.
- Symantec SoC Research – Specialist SoC researchers and researchers working on this platform. SOC Analyzer helps detect attacks and analyze malicious activity.
- Antivirus: Detect and remove malware.
- Barriers and obstruction. Monitor background traffic and prevent malware from spreading to other devices.
- Instructions and tools. Blocklist and allowlist for information, system documentation, licensing, and device performance monitoring.
- Power Off: Clean up remote areas by removing persistent threats (APTs) and malware.
- Check the honesty of the host. Verify the security and integrity of the solution, check for unauthorized changes, and find gaps.
- System Lock Option: Allow the blocklist system to close the system and run it usually automatically.
- Mobile user protection. Ensure complete and secure visibility of remote mobile devices. Avoid everything, whether mobile users are connected to company networks, other networks, or just them.
- Network Integrity Protection: Use the data to identify weak Wi-Fi networks.
- Smart VPN: Connect your device securely with a VPN based.
- The Global Information Network (GIN) is the world’s largest threat intelligence network, supported by millions of attack devices analyzed by Symantec’s threat analysis team. The most secure tool uses popular GIS analysis and machine learning to determine the security of files and websites.
- Simulator Sandbox – Simulator Sandbox Simulator Sandbox khadi had-wish ili trying to simulator sandbox changamano
- Surrender – No Foreclosure. Satish and sasisho hupakiwa make up 70% of the total Satish.
- Download from Windows Program Store or Simu Kifaa Cha Simu (MDM).
- Madame De for sale, along with வெஸும், రrrrrrr.
- Ram Ruhusu said, business administration and education, have this, and for the first time, kuchanganua hitilafu makosa. Programu zakutiliwa shaka au hasidi available in siw work and sleep.
- Responsibility is the sale of influence. An introduction to the planning and layout of the destination. Hii utta unyumbufu unaopetelan wajakada registration hall huku.Qatari
- Finally, pruning, kufichua audio aliyefichwa na kufichua za samadhi na hi tulo.
- Uchanganuzi na Majibu ya Mwisho (EDR) – Hutumia Intelligence Targeted Attack (TAA), Advanced Telemetry Department, uchanganuzi wa kuzizwa kwa mashine na akili ya kusommera ili Follow news. New version of TAA procedure and period, kiwa ni pamoja and guidance, tukho na kontaktu wa technika. EDR is the best place to visit.
- NGAV – Blockchain, Object Management, LOLBin, Macros, Malware.
- Usalama wa Siku Sifuri – Building base with UEBA during suspension.
- Plotting – plotting, plotting, them and them, them and them.
- Hear the word m. He marks it as core and provides answers to board responsibilities, design, and design.
- Akili ya Mkengeuko – Wahimize washomeraji Kwa council yanayoweza kuwa Hatari ili head and management manage the issue bodyna za kushameraji.
- Uchambuzi was Mukhowa – a Resident of Tafutu District, Kiidama Province, Myanmar.
System Requirements:
- Supported OS: Windows XP/Vista/7/8/8.1/10
- Memory Requirements (RAM): 256 MB RAM required (512 MB RAM recommended).
- Hard disk space required: 30 MB
- Processor: Intel Pentium 4 or higher.
- Right of owner
You May Also Like To Download: Avira Antivirus Pro Crack
You May Also Like To Download: Webroot Secureanywhere Antivirus Crack
Pros and Cons of Symantec Endpoint Protection Crack:
Symantec Endpoint Protection is a security software solution designed to protect endpoints such as desktops, laptops, and servers against malware, viruses, and other cyber threats. Here are some pros and cons of using Symantec Endpoint Protection:
Pros:
- Comprehensive protection: Symantec Endpoint Protection offers a broad range of protection features, including antivirus, firewall, intrusion prevention, and more, to ensure comprehensive protection against various cyber threats.
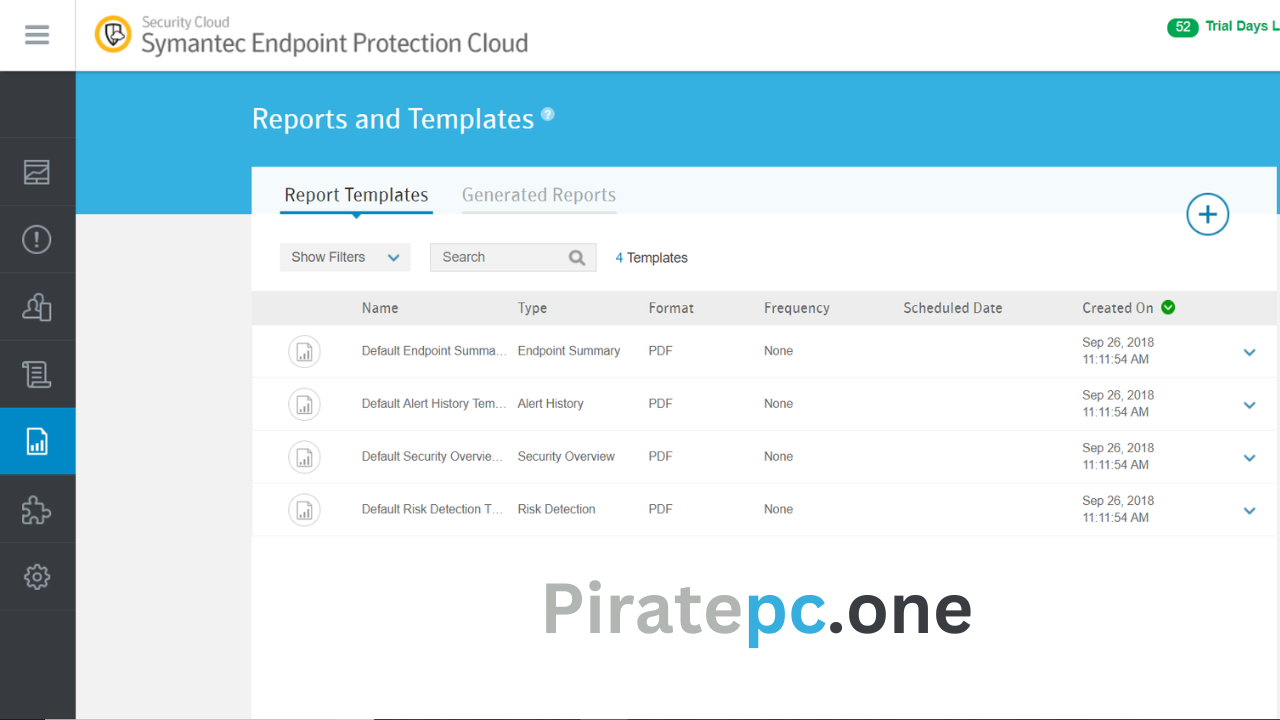
- Centralized management: The solution allows for centralized management, providing IT administrators with greater control and visibility into the organization’s security posture.
- Easy to use: Symantec Endpoint Protection is easy to use, with a simple interface that can be navigated easily even by non-technical users.
- Real-time protection: The solution offers real-time protection against threats, ensuring that endpoints are always protected against the latest malware and viruses.
- Scalability: Symantec Endpoint Protection is highly scalable, making it suitable for organizations of all sizes.
Cons:
- Resource-intensive: The software can be resource-intensive, causing some systems to slow down or experience performance issues, especially on older hardware.
- Limited reporting capabilities: Symantec Endpoint Protection has limited reporting capabilities, making it difficult for IT administrators to generate detailed reports on security events and incidents.
- Cost: The solution can be expensive, especially for small businesses that may not have the budget to invest in a comprehensive security solution.
- Compatibility issues: The software may not be compatible with some legacy systems or software applications, which can be a challenge for some organizations.
- False positives: Symantec Endpoint Protection may generate false positives, flagging legitimate files or applications as potential threats, which can be frustrating for users and IT administrators alike.
Overall, Symantec Endpoint Protection is a robust security solution that offers comprehensive protection against cyber threats. However, organizations should carefully consider the potential drawbacks, such as resource usage and compatibility issues, before implementing the solution.
How To Install And Download:
- First, download this software from the torrent link below.
- After downloading, the user must install the Windows software.
- No hooks or brackets are needed after installation.
- This program is pre-programmed. Open the app and start searching.
Download Now:
FAQS OF Symantec Endpoint Protection Crack:
Here are some frequently asked questions (FAQs) about Symantec Endpoint Protection:
Q: What is Symantec Endpoint Protection?
A: Symantec Endpoint Protection is a security software solution designed to protect endpoints such as desktops, laptops, and servers against malware, viruses, and other cyber threats. The software includes a range of protection features, including antivirus, firewall, intrusion prevention, and more.
Q: How does Symantec Endpoint Protection work?
A: Symantec Endpoint Protection works by monitoring network traffic and system activity to detect and prevent threats. The software uses a combination of signature-based detection, behavioral analysis, and machine learning to identify and block malware and other cyber threats.
Q: What platforms does Symantec Endpoint Protection support?
A: Symantec Endpoint Protection supports a range of platforms, including Windows, macOS, Linux, and virtual environments.
Q: What are some of the features of Symantec Endpoint Protection?
A: Symantec Endpoint Protection includes a broad range of protection features, including antivirus, firewall, intrusion prevention, device control, application control, and more. The software also offers centralized management capabilities, automatic updates and security patches, and real-time protection against threats.
Q: What are the system requirements for Symantec Endpoint Protection?
A: The system requirements for Symantec Endpoint Protection vary depending on the platform and version of the software. However, generally, the software requires a modern processor, at least 2 GB of RAM, and several hundred MB of disk space.
Q: How does Symantec Endpoint Protection compare to other security solutions?
A: Symantec Endpoint Protection is a comprehensive security solution that offers a broad range of protection features and centralized management capabilities. It compares favorably to other security solutions in terms of effectiveness, ease of use, and scalability.
Q: Does Symantec Endpoint Protection offer support and training?
A: Yes, Symantec offers support for Symantec Endpoint Protection, including online documentation, community forums, and technical support. The company also offers training and certification programs to help IT professionals better understand and manage the solution.
Q: Is Symantec Endpoint Protection suitable for small businesses?
A: Yes, Symantec Endpoint Protection is suitable for small businesses. The software is scalable and can be customized to meet the needs of organizations of all sizes. However, small businesses may want to consider the cost of the software when making a purchasing decision.
